The technologies, methodologies, and paradigms that have shaped the way software is designed, built, and delivered have evolved from the Waterfall model, proposed in 1970 by Dr. Winston W. Royce to Agile model in early 2000. The Waterfall model was characterized by sequential and rigid phases, detailed documentation, and milestone-based progression and suffered from inflexibility to adapt to changes, longer time-to-market, high risk and uncertainty difficulty in accurately estimating costs and time, silos between teams, and late discovery of issues. The Agile model addresses these shortcomings by adopting iterative and incremental development, continuous delivery, feedback loops, lower risk, and cross-functional teams. In addition, modern software development process over the last few years have adopted DevOps integration, automated testing, microservices and modular architecture, cloud services, infrastructure as code, and data driven decisions to improve the time to market, customer satisfaction, cost efficiency, operational resilience, collaboration, and sustainable development.

1. Goals
The goals of modern software development process includes:
- Speed and Agility: Accelerate the delivery of high-quality software products and updates to respond to market demands and user needs.
- Quality and Reliability: Ensure that the software meets specified requirements, performs reliably under all conditions, and is maintainable and scalable.
- Reduced Complexity: Simplify complex tasks with use of refactoring and microservices.
- Customer-Centricity: Develop features and products that solve real problems for users and meet customer expectations for usability and experience.
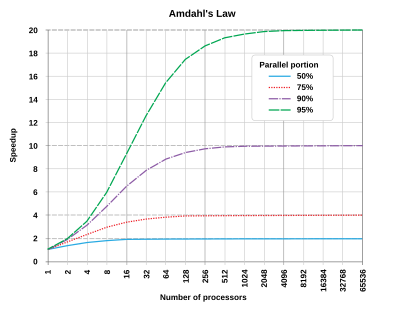
- Scalability: Design software that can grow and adapt to changing user needs and technological advancements.
- Cost-Efficiency: Optimize resource utilization and operational costs through automation and efficient practices.
- Security: Ensure the integrity, availability, and confidentiality of data and services.
- Innovation: Encourage a culture of innovation and learning, allowing teams to experiment, iterate, and adapt.
- Collaboration and Transparency: Foster a collaborative environment among cross-functional teams and maintain transparency with stakeholders.
- Employee Satisfaction: Focus on collaboration, autonomy, and mastery can lead to more satisfied, motivated teams.
- Learning and Growth: Allows teams to reflect on their wins and losses regularly, fostering a culture of continuous improvement.
- Transparency: Promote transparency with regular meetings like daily stand-ups and sprint reviews.
- Flexibility: Adapt to changes even late in the development process.
- Compliance and Governance: Ensure that software meets industry-specific regulations and standards.
- Risk Mitigation: Make it easier to course-correct, reducing the risk of late project failure.
- Competitive Advantage: Enables companies to adapt to market changes more swiftly, offering a competitive edge.
2. Elements of Software Development Process
Key elements of the Software Development Cycle include:
- Discovery & Ideation: Involves brainstorming, feasibility studies, and stakeholder buy-in. Lean startup methodologies might be applied for new products.
- Continuous Planning: Agile roadmaps, iterative sprint planning, and backlog refinement are continuous activities.
- User-Centric Design: The design process is iterative, human-centered, and closely aligned with development.
- Development & Testing: Emphasizes automated testing, code reviews, and incremental development. CI/CD pipelines automate much of the build and testing process.
- Deployment & Monitoring: DevOps practices facilitate automated, reliable deployments. Real-time monitoring tools and AIOps (Artificial Intelligence for IT Operations) can proactively manage system health.
- Iterative Feedback Loops: Customer feedback, analytics, and KPIs inform future development cycles.
3. Roles in Modern Processes
Critical Roles in Contemporary Software Development include:
- Product Owner/Product Manager: This role serves as the liaison between the business and technical teams. They are responsible for defining the product roadmap, prioritizing features, and ensuring that the project aligns with stakeholder needs and business objectives.
- Scrum Master/Agile Coach: These professionals are responsible for facilitating Agile methodologies within the team. They help organize and run sprint planning sessions, stand-ups, and retrospectives.
- Development Team: This group is made up of software engineers and developers responsible for the design, coding, and initial testing of the product. They collaborate closely with other roles, especially the Product Owner, to ensure that the delivered features meet the defined requirements.
- DevOps Engineers: DevOps Engineers act as the bridge between the development and operations teams. They focus on automating the Continuous Integration/Continuous Deployment (CI/CD) pipeline to ensure that code can be safely, efficiently, and reliably moved from development into production.
- QA Engineers: Quality Assurance Engineers play a vital role in the software development life cycle by creating automated tests that are integrated into the CI/CD pipeline.
- Data Scientists: These individuals use analytical techniques to draw actionable insights from data generated by the application. They may look at user behavior, application performance, or other metrics to provide valuable feedback that can influence future development cycles or business decisions.
- Security Engineers: Security Engineers are tasked with ensuring that the application is secure from various types of threats. They are involved from the early stages of development to ensure that security is integrated into the design (“Security by Design”).
Each of these roles plays a critical part in modern software development, contributing to more efficient processes, higher-quality output, and ultimately, greater business value.
4. Phases of Modern SDLC
In the Agile approach to the software development lifecycle, multiple phases are organized not in a rigid, sequential manner as seen in the Waterfall model, but as part of a more fluid, iterative process. This allows for continuous feedback loops and enables incremental delivery of features. Below is an overview of the various phases that constitute the modern Agile-based software development lifecycle:
4.1 Inception Phase
The Inception phase is the initial stage in a software development project, often seen in frameworks like the Rational Unified Process (RUP) or even in Agile methodologies in a less formal manner. It sets the foundation for the entire project by defining its scope, goals, constraints, and overall vision.
4.1.1 Objectives
The objectives of inception phase includes:
- Project Vision and Scope: Define what the project is about, its boundaries, and what it aims to achieve.
- Feasibility Study: Assess whether the project is feasible in terms of time, budget, and technical constraints.
- Stakeholder Identification: Identify all the people or organizations who have an interest in the project, such as clients, end-users, developers, and more.
- Risk Assessment: Evaluate potential risks, like technical challenges, resource limitations, and market risks, and consider how they can be mitigated.
- Resource Planning: Preliminary estimation of the resources (time, human capital, budget) required for the project.
- Initial Requirements Gathering: Collect high-level requirements, often expressed as epics or user stories, which will be refined later.
- Project Roadmap: Create a high-level project roadmap that outlines major milestones and timelines.
4.1.2 Practices
The inception phase includes following practices:
- Epics Creation: High-level functionalities and features are described as epics.
- Feasibility Study: Analyze the technical and financial feasibility of the proposed project.
- Requirements: Identify customers and document requirements that were captured from the customers. Review requirements with all stakeholders and get alignment on key features and deliverables. Be careful for a scope creep so that the software change can be delivered incrementally.
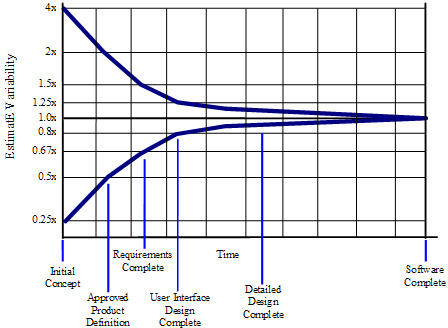
- Estimated Effort: A high-level effort in terms of estimated man-month, t-shirt size, or story-points to build and deliver the features.
- Business Metrics: Define key business metrics that will be tracked such as adoption, utilization and success criteria for the features.
- Customer and Dependencies Impact: Understand how the changes will impact customers as well as upstream/downstream dependencies.
- Roadmapping: Develop a preliminary roadmap to guide the project’s progression.
4.1.3 Roles and Responsibilities:
The roles and responsibilities in inception phase include:
- Stakeholders: Validate initial ideas and provide necessary approvals or feedback.
- Product Owner: Responsible for defining the vision and scope of the product, expressed through a set of epics and an initial product backlog. The product manager interacts with customers, defines the customer problems and works with other stakeholders to find solutions. The product manager defines end-to-end customer experience and how the customer will benefit from the proposed solution.
- Scrum Master: Facilitates the Inception meetings and ensures that all team members understand the project’s objectives and scope. The Scrum master helps write use-cases, user-stories and functional/non-functional requirements into the Sprint Backlog.
- Development Team: Provide feedback on technical feasibility and initial estimates for the project scope.
By carefully executing the Inception phase, the team can ensure that everyone has a clear understanding of the ‘what,’ ‘why,’ and ‘how’ of the project, thereby setting the stage for a more organized and focused development process.
4.2. Planning Phase
The Planning phase is an essential stage in the Software Development Life Cycle (SDLC), especially in methodologies that adopt Agile frameworks like Scrum or Kanban. This phase aims to detail the “how” of the project, which is built upon the “what” and “why” established during the Inception phase. The Planning phase involves specifying objectives, estimating timelines, allocating resources, and setting performance measures, among other activities.
4.2.1 Objectives
The objectives of planning phase includes:
- Sprint Planning: Determine the scope of the next sprint, specifying what tasks will be completed.
- Release Planning: Define the features and components that will be developed and released in the upcoming iterations.
- Resource Allocation: Assign tasks and responsibilities to team members based on skills and availability.
- Timeline and Effort Estimation: Define the timeframe within which different tasks and sprints should be completed.
- Risk Management: Identify, assess, and plan for risks and contingencies.
- Technical Planning: Decide the architectural layout, technologies to be used, and integration points, among other technical aspects.
4.2.2 Practices:
The planning phase includes following practices:
- Sprint Planning: A meeting where the team decides what to accomplish in the coming sprint.
- Release Planning: High-level planning to set goals and timelines for upcoming releases.
- Backlog Refinement: Ongoing process to add details, estimates, and order to items in the Product Backlog.
- Effort Estimation: Techniques like story points, t-shirt sizes, or time-based estimates to assess how much work is involved in a given task or story.
4.2.3 Roles and Responsibilities:
The roles and responsibilities in planning phase include:
- Product Owner: Prioritizes the Product Backlog and clarifies details of backlog items. Helps the team understand which items are most crucial to the project’s success.
- Scrum Master: Facilitates planning meetings and ensures that the team has what they need to complete their tasks. Addresses any impediments that the team might face.
- Development Team: Provides effort estimates for backlog items, helps break down stories into tasks, and commits to the amount of work they can accomplish in the next sprint.
- Stakeholders: May provide input on feature priority or business requirements, though they typically don’t participate in the detailed planning activities.
4.2.4 Key Deliverables:
Key deliverables in planning phase include:
- Sprint Backlog: A list of tasks and user stories that the development team commits to complete in the next sprint.
- Execution Plan: A plan outlining the execution of the software development including dependencies from other teams. The plan also identifies key reversible and irreversible decisions.
- Deployment and Release Plan: A high-level plan outlining the features and major components to be released over a series of iterations. This plan also includes feature flags and other configuration parameters such as throttling limits.
- Resource Allocation Chart: A detailed breakdown of who is doing what.
- Risk Management Plan: A documentation outlining identified risks, their severity, and mitigation strategies.
By thoroughly engaging in the Planning phase, teams can have a clear roadmap for what needs to be achieved, how it will be done, who will do it, and when it will be completed. This sets the project on a course that maximizes efficiency, minimizes risks, and aligns closely with the stakeholder requirements and business objectives.
4.3. Design Phase
The Design phase in the Software Development Life Cycle (SDLC) is a critical step that comes after planning and before coding. During this phase, the high-level architecture and detailed design of the software system are developed. This serves as a blueprint for the construction of the system, helping the development team understand how the software components will interact, what data structures will be used, and how user interfaces will be implemented, among other things.
4.3.1 Objectives:
The objectives of design phase includes:
- Architectural Design: Define the software’s high-level structure and interactions between components. Understand upstream and downstream dependencies and how architecture decisions affect those dependencies. The architecture will ensure scalability to a minimum of 2x of the peak traffic and will build redundancy to avoid single points of failure. The architecture decisions should be documented in an Architecture Decision Record format and should be defined in terms of reversible and irreversible decisions.
- Low-Level Design: Break down the architectural components into detailed design specifications including functional and non-functional considerations. The design documents should include alternative solutions and tradeoffs when selecting a recommended approach. The design document should consider how the software can be delivered incrementally and whether multiple components can be developed in parallel. Other best practices such as not breaking backward compatibility, composable modules, consistency, idempotency, pagination, no unbounded operations, validation, and purposeful design should be applied to the software design.
- API Design: Specify the endpoints, request/response models, and the underlying architecture for any APIs that the system will expose.
- User Interface Design: Design the visual elements and user experiences.
- Data Model Design: Define the data structures and how data will be stored, accessed, and managed.
- Functional Design: Elaborate on the algorithms, interactions, and methods that will implement software features.
- Security Design: Implement security measures like encryption, authentication, and authorization.
- Performance Considerations: Design for scalability, reliability, and performance optimization.
- Design for Testability: Ensure elements can be easily tested.
- Operational Excellence: Document monitoring, logging, operational and business metrics, alarms, and dashboards to monitor health of the software components.
4.3.2 Practices:
The design phase includes following practices:
- Architectural and Low-Level Design Reviews: Conducted to validate the robustness, scalability, and performance of the design. High-level reviews focus on the system architecture, while low-level reviews dig deep into modules, classes, and interfaces.
- API Design Review: A specialized review to ensure that the API design adheres to RESTful principles, is consistent, and meets performance and security benchmarks.
- Accessibility Review: Review UI for accessibility support.
- Design Patterns: Utilize recognized solutions for common design issues.
- Wireframing and Prototyping: For UI/UX design.
- Sprint Zero: Sometimes used in Agile for initial setup, including design activities.
- Backlog Refinement: Further details may be added to backlog items in the form of acceptance criteria and design specs.
4.3.3 Roles and Responsibilities:
The roles and responsibilities in design phase include:
- Product Owner: Defines the acceptance criteria for user stories and validates that the design meets business and functional requirements.
- Scrum Master: Facilitates design discussions and ensures that design reviews are conducted effectively.
- Development Team: Creates the high-level architecture, low-level detailed design, and API design. Chooses design patterns and data models.
- UX/UI Designers: Responsible for user interface and user experience design.
- System Architects: Involved in high-level design and may also review low-level designs and API specifications.
- API Designers: Specialized role focusing on API design aspects such as endpoint definition, rate limiting, and request/response models.
- QA Engineers: Participate in design reviews to ensure that the system is designed for testability.
- Security Engineers: Involved in both high-level and low-level design reviews to ensure that security measures are adequately implemented.
4.3.4 Key Deliverables:
Key deliverables in design phase include:
- High-Level Architecture Document: Describes the architectural layout and high-level components.
- Low-Level Design Document: Provides intricate details of each module, including pseudo-code, data structures, and algorithms.
- API Design Specification: Comprehensive documentation for the API including endpoints, methods, request/response formats, and error codes.
- Database Design: Includes entity-relationship diagrams, schema designs, etc.
- UI Mockups: Prototypes or wireframes of the user interface.
- Design Review Reports: Summaries of findings from high-level, low-level, and API design reviews.
- Proof of Concept and Spikes: Build proof of concepts or execute spikes to learn about high risk design components.
- Architecture Decision Records: Documents key decisions that were made including tradeoffs, constraints, stakeholders and final decision.
The Design phase serves as the blueprint for the entire project. Well-thought-out and clear design documentation helps mitigate risks, provides a clear vision for the development team, and sets the stage for efficient and effective coding, testing, and maintenance.
4.4 Development Phase
The Development phase in the Software Development Life Cycle (SDLC) is the stage where the actual code for the software is written, based on the detailed designs and requirements specified in the preceding phases. This phase involves coding, unit testing, integration, and sometimes even preliminary system testing to validate that the implemented features meet the specifications.
4.4.1 Objectives:
The objectives of development phase includes:
- Coding: Translate design documentation and specifications into source code.
- Modular Development: Build the software in chunks or modules for easier management, testing, and debugging.
- Unit Testing: Verify that each unit or module functions as designed.
- Integration: Combine separate units and modules into a single, functioning system.
- Code Reviews: Validate that code adheres to standards, guidelines, and best practices.
- Test Plans: Review test plans for all test-cases that will validate the changes to the software.
- Documentation: Produce inline code comments, READMEs, and technical documentation.
- Early System Testing: Sometimes, a form of system testing is performed to catch issues early.
4.4.2 Practices:
The development phase includes following practices:
- Pair Programming: Two developers work together at one workstation, enhancing code quality.
- Test-Driven Development (TDD): Write failing tests before writing code, then write code to pass the tests.
- Code Reviews: Peer reviews to maintain code quality.
- Continuous Integration: Frequently integrate code into a shared repository and run automated tests.
- Version Control: Use of tools like Git to manage changes and history.
- Progress Report: Use of burndown charts, risk analysis, blockers and other data to apprise stakeholders up-to-date with the progress of the development effort.
4.4.3 Roles and Responsibilities:
The roles and responsibilities in development phase include:
- Product Owner: Prioritizes features and stories in the backlog that are to be developed, approves or rejects completed work based on acceptance criteria.
- Scrum Master: Facilitates daily stand-ups, removes impediments, and ensures the team is focused on the tasks at hand.
- Software Developers: Write the code, perform unit tests, and integrate modules.
- QA Engineers: Often involved early in the development phase to write automated test scripts, and to run unit tests along with developers.
- DevOps Engineers: Manage the CI/CD pipeline to automate code integration and preliminary testing.
- Technical Leads/Architects: Provide guidance and review code to ensure it aligns with architectural plans.
4.4.4 Key Deliverables:
Key deliverables in development phase include:
- Source Code: The actual code files, usually stored in a version control system.
- Unit Test Cases and Results: Documentation showing what unit tests have been run and their results.
- Code Review Reports: Findings from code reviews.
- Technical Documentation: Sometimes known as codebooks or developer guides, these detail how the code works for future maintenance.
4.4.5 Best Practices for Development:
Best practices in development phase include:
- Clean Code: Write code that is easy to read, maintain, and extend.
- Modularization: Build in a modular fashion for ease of testing, debugging, and scalability.
- Commenting and Documentation: In-line comments and external documentation to aid in future maintenance and understanding.
- Code Repositories: Use version control systems to keep a historical record of all changes and to facilitate collaboration.
The Development phase is where the design and planning turn into a tangible software product. Following best practices and guidelines during this phase can significantly impact the quality, maintainability, and scalability of the end product.
4.5. Testing Phase
The Testing phase in the Software Development Life Cycle (SDLC) is crucial for validating the system’s functionality, performance, security, and stability. This phase involves various types of testing methodologies to ensure that the software meets all the requirements and can handle expected and unexpected situations gracefully.
4.5.1 Objectives:
The objectives of testing phase includes:
- Validate Functionality: Ensure all features work as specified in the requirements.
- Ensure Quality: Confirm that the system is reliable, secure, and performs optimally.
- Identify Defects: Find issues that need to be addressed before the software is deployed.
- Risk Mitigation: Assess and mitigate potential security and performance risks.
4.5.2 Practices:
The testing phase includes following practices:
- Test Planning: Create a comprehensive test plan detailing types of tests, scope, schedule, and responsibilities.
- Test Case Design: Prepare test cases based on various testing requirements.
- Test Automation: Automate repetitive and time-consuming tests.
- Continuous Testing: Integrate testing into the CI/CD pipeline for continuous feedback.
4.5.3 Types of Testing and Responsibilities:
The test phase includes following types of testing:
- Integration Testing:
Responsibilities: QA Engineers, DevOps Engineers
Objective: Verify that different modules or services work together as expected. - Functional Testing:
Responsibilities: QA Engineers
Objective: Validate that the system performs all the functions as described in the specifications. - Load/Stress Testing:
Responsibilities: Performance Test Engineers, DevOps Engineers
Objective: Check how the system performs under heavy loads. - Security and Penetration Testing:
Responsibilities: Security Engineers, Ethical Hackers
Objective: Identify vulnerabilities that an attacker could exploit. - Canary Testing:
Responsibilities: DevOps Engineers, Product Owners
Objective: Validate that new features or updates will perform well with a subset of the production environment before full deployment. - Other Forms of Testing:
Smoke Testing: Quick tests to verify basic functionality after a new build or deployment.
Regression Testing: Ensure new changes haven’t adversely affected existing functionalities.
User Acceptance Testing (UAT): Final validation that the system meets business needs, usually performed by stakeholders or end-users.
4.5.4 Key Deliverables:
- Test Plan: Describes the scope, approach, resources, and schedule for the testing activities.
- Test Cases: Detailed description of what to test, how to test, and expected outcomes.
- Test Scripts: Automated scripts for testing.
- Test Reports: Summary of testing activities, findings, and results.
4.5.5 Best Practices for Testing:
- Early Involvement: Involve testers from the early stages of SDLC for better understanding and planning.
- Code Reviews: Conduct code reviews to catch potential issues before the testing phase.
- Data-Driven Testing: Use different sets of data to evaluate how the application performs with various inputs.
- Monitoring and Feedback Loops: Integrate monitoring tools to get real-time insights during testing and improve the test scenarios continuously.
The Testing phase is crucial for delivering a reliable, secure, and robust software product. The comprehensive testing strategy that includes various types of tests ensures that the software is well-vetted before it reaches the end-users.
4.6. Deployment Phase
The Deployment phase in the Software Development Life Cycle (SDLC) involves transferring the well-tested codebase from the staging environment to the production environment, making the application accessible to the end-users. This phase aims to ensure a smooth transition of the application from development to production with minimal disruptions and optimal performance.
4.6.1 Objectives:
The objectives of deployment phase includes:
- Release Management: Ensure that the application is packaged and released properly.
- Transition: Smoothly transition the application from staging to production.
- Scalability: Ensure the infrastructure can handle the production load.
- Rollback Plans: Prepare contingencies for reverting changes in case of failure.
4.6.2 Key Components and Practices:
The key components and practices in deployment phase include:
- Continuous Deployment (CD):
Responsibilities: DevOps Engineers, QA Engineers, Developers
Objective: Automatically deploy all code changes to the production environment that pass the automated testing phase.
Tools: Jenkins, GitLab CI/CD, GitHub Actions, Spinnaker - Infrastructure as Code (IaC):
Responsibilities: DevOps Engineers, System Administrators
Objective: Automate the provisioning and management of infrastructure using code.
Tools: Terraform, AWS CloudFormation, Ansible - Canary Testing:
Responsibilities: DevOps Engineers, QA Engineers
Objective: Gradually roll out the new features to a subset of users before a full-scale rollout to identify potential issues. - Phased Deployment:
Responsibilities: DevOps Engineers, Product Managers
Objective: Deploy the application in phases to monitor its stability and performance, enabling easier troubleshooting. - Rollback:
Responsibilities: DevOps Engineers
Objective: Be prepared to revert the application to its previous stable state in case of any issues. - Feature Flags:
Responsibilities: Developers, Product Managers
Objective: Enable or disable features in real-time without deploying new code. - Resilience:
Responsibilities: DevOps Engineers, Developers
Objective: Prevent retry storms, throttle the number of client requests, and apply reliability patterns such as Circuit Breakers and BulkHeads. Avoid bimodal behavior and maintain software latency and throughput within the defined SLAs. - Scalability:
Responsibilities: DevOps Engineers, Developers
Objective: Monitor scalability limits and implement elastic scalability. Review scaling limits periodically. - Throttling and Sharding Limits (and other Configurations):
Responsibilities: DevOps Engineers, Developers
Objective: Review configuration and performance configurations such as throttling and sharding limits. - Access Policies:
Responsibilities: DevOps Engineers, Developers
Objective: Review access policies, permissions and roles that can access the software.
4.6.3 Roles and Responsibilities:
The deployment phase includes following roles and responsibilities:
- DevOps Engineers: Manage CI/CD pipelines, IaC, and automate deployments.
- Product Managers: Approve deployments based on feature completeness and business readiness.
- QA Engineers: Ensure the application passes all tests in the staging environment before deployment.
- System Administrators: Ensure that the infrastructure is ready and scalable for deployment.
4.6.4 Key Deliverables:
The deployment phase includes following key deliverables:
- Deployment Checklist: A comprehensive list of tasks and checks before, during, and after deployment.
- CD Pipeline Configuration: The setup details for the Continuous Deployment pipeline.
- Automated Test Cases: Essential for validating the application before automatic deployment.
- Operational, Security and Compliance Review Documents: These documents will define checklists about operational excellence, security and compliance support in the software.
- Deployment Logs: Automated records of what was deployed, when, and by whom (usually by the automation system).
- Logging: Review data that will be logged and respective log levels so that data privacy is not violated and excessive logging is avoided.
- Deployment Schedule: A timeline for the deployment process.
- Observability: Health dashboard to monitor operational and business metrics, and alarms to receive notifications when service-level-objectives (SLO) are violated. The operational metrics will include availability, latency, and error metrics. The health dashboard will monitor utilization of CPU, disk space, memory, and network resources.
- Rollback Plan: A detailed plan for reverting to the previous stable version if necessary.
4.6.5 Best Practices:
Following are a few best practices for the deployment phase:
- Automated Deployments: Use automation tools for deployment of code and infrastructure to minimize human error.
- Monitoring and Alerts: Use monitoring tools to get real-time insights into application performance and set up alerts for anomalies.
- Version Control: Ensure that all deployable artifacts are versioned for traceability.
- Comprehensive Testing: Given the automated nature of Continuous Deployment, having a comprehensive suite of automated tests is crucial.
- Rollback Strategy: Have an automated rollback strategy in case the new changes result in system failures or critical bugs.
- Feature Toggles: Use feature flags to control the release of new features, which can be enabled or disabled without having to redeploy.
- Audit Trails: Maintain logs and history for compliance and to understand what was deployed and when.
- Documentation: Keep detailed records of the deployment process, configurations, and changes.
- Stakeholder Communication: Keep all stakeholders in the loop regarding deployment schedules, success, or issues.
- Feedback from Early Adopters: If the software is being released to internal or a beta customers, then capture feedback from those early adopters including any bugs report.
- Marketing and external communication: The release may need to be coordinated with a marketing campaign so that customers can be notified about new features.
The Deployment phase is critical for ensuring that the software is reliably and securely accessible by the end-users. A well-planned and executed deployment strategy minimizes risks and disruptions, leading to a more dependable software product.
4.7 Maintenance Phase
The Maintenance phase in the Software Development Life Cycle (SDLC) is the ongoing process of ensuring the software’s continued effective operation and performance after its release to the production environment. The objective of this phase is to sustain the software in a reliable state, provide continuous support, and make iterative improvements or patches as needed.
4.7.1 Objectives:
The objectives of maintenance phase includes:
- Bug Fixes: Address any issues or defects that arise post-deployment.
- Updates & Patches: Release minor or major updates and patches to improve functionality or security.
- Optimization: Tune the performance of the application based on metrics and feedback.
- Scalability: Ensure that the software can handle growth in terms of users, data, and transaction volume.
- Documentation: Update all documents related to software changes and configurations.
4.7.2 Key Components and Practices:
The key components and practices of maintenance phase include:
- Incident Management:
Responsibilities: Support Team, DevOps Engineers
Objective: Handle and resolve incidents affecting the production environment. - Technical Debt Management:
Responsibilities: Development Team, Product Managers
Objective: Prioritize and resolve accumulated technical debt to maintain code quality and performance. - Security Updates:
Responsibilities: Security Engineers, DevOps Engineers
Objective: Regularly update and patch the software to safeguard against security vulnerabilities. - Monitoring & Analytics:
Responsibilities: DevOps Engineers, Data Analysts
Objective: Continuously monitor software performance, availability, and usage to inform maintenance tasks. - Documentation and Runbooks:
Responsibilities: Support Team, DevOps Engineers
Objective: Define cookbooks for development processes and operational issues.
4.7.3 Roles and Responsibilities:
The maintenance phase includes following roles and responsibilities:
- DevOps Engineers: Monitor system health, handle deployments for updates, and coordinate with the support team for incident resolution.
- Support Team: Provide customer support, report bugs, and assist in reproducing issues for the development team.
- Development Team: Develop fixes, improvements, and updates based on incident reports, performance metrics, and stakeholder feedback.
- Product Managers: Prioritize maintenance tasks based on customer needs, business objectives, and technical requirements.
- Security Engineers: Regularly audit the software for vulnerabilities and apply necessary security patches.
4.7.4 Key Deliverables:
Key deliverables for the maintenance phase include:
- Maintenance Plan: A detailed plan outlining maintenance activities, schedules, and responsible parties.
- Patch Notes: Documentation describing what has been fixed or updated in each new release.
- Performance Reports: Regular reports detailing the operational performance of the software.
4.7.5 Best Practices for Maintenance:
Following are a few best practices for the maintenance phase:
- Automated Monitoring: Use tools like Grafana, Prometheus, or Zabbix for real-time monitoring of system health.
- Feedback Loops: Use customer feedback and analytics to prioritize maintenance activities.
- Version Control: Always version updates and patches for better tracking and rollback capabilities.
- Knowledge Base: Maintain a repository of common issues and resolutions to accelerate incident management.
- Scheduled Maintenance: Inform users about planned downtimes for updates and maintenance activities.
The Maintenance phase is crucial for ensuring that the software continues to meet user needs and operate effectively in the ever-changing technical and business landscape. Proper maintenance ensures the longevity, reliability, and continual improvement of the software product. Also, note that though maintenance is defined as a separate phase above but it will include other phases from inception to deployment and each change will be developed and deployed incrementally in iterative agile process.
5. Best Practices for Ensuring Reliability, Quality, and Incremental Delivery
Following best practices ensure incremental delivery with higher reliability and quality:
5.1. Iterative Development:
Embrace the Agile principle of delivering functional software frequently. The focus should be on breaking down the product into small, manageable pieces and improving it in regular iterations, usually two to four-week sprints.
- Tools & Techniques: Feature decomposition, Sprint planning, Short development cycles.
- Benefits: Faster time to market, easier bug isolation, and tracking, ability to incorporate user feedback quickly.
5.2. Automated Testing:
Implement Test-Driven Development (TDD) or Behavior-Driven Development (BDD) to script tests before the actual coding begins. Maintain these tests to run automatically every time a change is made.
- Tools & Techniques: JUnit, Selenium, Cucumber.
- Benefits: Instant feedback on code quality, regression testing, enhanced code reliability.
5.3. Design Review:
- Detailed Explanation: A formal process where architects and developers evaluate high-level and low-level design documents to ensure they meet the project requirements, are scalable, and adhere to best practices.
- Tools & Techniques: Design diagrams, UML, Peer Reviews, Design Review Checklists.
- Benefits: Early identification of design flaws, alignment with stakeholders, consistency across the system architecture.
5.4 Code Reviews:
Before any code gets merged into the main repository, it should be rigorously reviewed by other developers to ensure it adheres to coding standards, is optimized, and is free of bugs.
- Tools & Techniques: Git Pull Requests, Code Review Checklists, Pair Programming.
- Benefits: Team-wide code consistency, early detection of anti-patterns, and a secondary check for overlooked issues.
5.5 Security Review:
A comprehensive evaluation of the security aspects of the application, involving both static and dynamic analyses, is conducted to identify potential vulnerabilities.
- Tools & Techniques: OWASP Top 10, Security Scanners like Nessus or Qualys, Code Review tools like Fortify, Penetration Testing.
- Benefits: Proactive identification of security vulnerabilities, adherence to security best practices, and compliance with legal requirements.
5.6 Operational Review:
Before deploying any new features or services, assess the readiness of the operational environment, including infrastructure, data backup, monitoring, and support plans.
- Tools & Techniques: Infrastructure as Code tools like Terraform, Monitoring tools like Grafana, Documentation.
- Benefits: Ensures the system is ready for production, mitigates operational risks, confirms that deployment and rollback strategies are in place.
5.7 CI/CD (Continuous Integration and Continuous Deployment):
Integrate all development work frequently and deliver changes to the end-users reliably and rapidly using automated pipelines.
- Tools & Techniques: Jenkins, GitLab CI/CD, Docker, Kubernetes.
- Benefits: Quicker discovery of integration bugs, reduced lead time for feature releases, and improved deployability.
5.8 Monitoring:
Implement sophisticated monitoring tools that continuously observe system performance, user activity, and operational health.
- Tools & Techniques: Grafana, Prometheus, New Relic.
- Benefits: Real-time data analytics, early identification of issues, and rich metrics for performance tuning.
5.9 Retrospectives:
At the end of every sprint or project phase, the team should convene to discuss what worked well, what didn’t, and how processes can be improved.
- Tools & Techniques: Post-its for brainstorming, Sprint Retrospective templates, Voting mechanisms.
- Benefits: Continuous process improvement, team alignment, and reflection on the project’s success and failures.
5.10 Product Backlog Management:
A live document containing all known requirements, ranked by priority and constantly refined to reflect changes and learnings.
- Tools & Techniques: JIRA, Asana, Scrum boards.
- Benefits: Focused development on high-impact features, adaptability to market or user needs.
5.11. Kanban for Maintenance:
For ongoing maintenance work and technical debt management, utilize a Kanban system to visualize work, limit work-in-progress, and maximize efficiency.
- Tools & Techniques: Kanban boards, JIRA Kanban, Trello.
- Benefits: Dynamic prioritization, quicker task completion, and efficient resource utilization.
5.12 Feature Flags:
Feature flags allow developers to toggle the availability of certain functionalities without deploying new versions.
- Tools & Techniques: LaunchDarkly, Config files, Custom-built feature toggles.
- Benefits: Risk mitigation during deployments, simpler rollbacks, and fine-grained control over feature releases.
5.13 Documentation:
Create comprehensive documentation, ranging from code comments and API docs to high-level architecture guides and FAQs for users.
- Tools & Techniques: Wiki platforms, OpenAPI/Swagger for API documentation, Code comments.
- Benefits: Streamlined onboarding for new developers, easier troubleshooting, and long-term code maintainability.
By diligently applying these multi-layered Agile best practices and clearly defined roles, your SDLC will be a well-oiled machine—more capable of rapid iterations, quality deliverables, and high adaptability to market or user changes.
6. Conclusion
The Agile process combined with modern software development practices offers an integrated and robust framework for building software that is adaptable, scalable, and high-quality. This approach is geared towards achieving excellence at every phase of the Software Development Life Cycle (SDLC), from inception to deployment and maintenance. The key benefits of this modern software development process includes flexibility and adaptability, reduced time-to-market, enhanced quality, operational efficiency, risk mitigation, continuous feedback, transparency, collaboration, cost-effectiveness, compliance and governance, and documentation for sustainment. By leveraging these Agile and modern software development practices, organizations can produce software solutions that are not only high-quality and reliable but also flexible enough to adapt to ever-changing requirements and market conditions.